Introduction
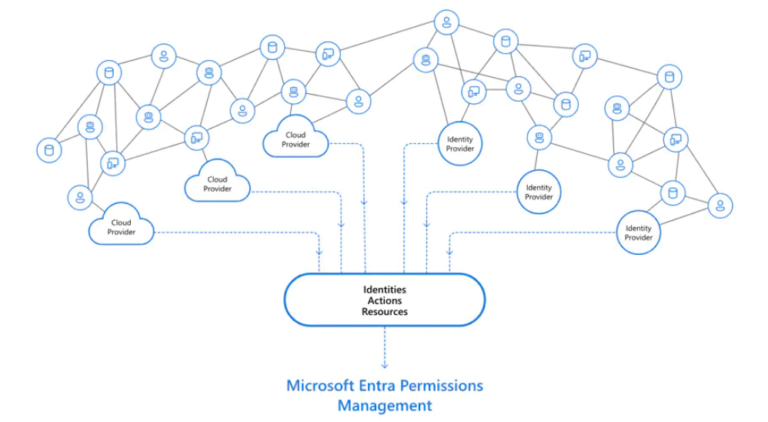
Microsoft Entra Permissions Management is a cloud infrastructure entitlement management (CIEM) product that provides comprehensive visibility and control over permissions for any identity and any resource in Microsoft Azure, Amazon Web Services (AWS), and Google Cloud Platform (GCP). One of the key features of Entra PM is its ability to operate in “Controller” mode, which enables you to make changes to your Azure environment directly through the Entra PM interface.
In this blog post, we will explore the capabilities of the “Controller” mode and demonstrate how you can leverage it to monitor and manage permissions in your Azure environment effectively.
Understanding Entra PM “Controller” Mode
In “Controller” mode, Entra PM utilizes a single Enterprise Application to manage permissions across your Azure environment. This application acts as an intermediary between Entra PM and Azure, enabling you to monitor and control access to resources, users, and groups in a centralized manner. By using the “Controller” mode, administrators can simplify the process of managing access control, streamline workflows, and improve the security of their Azure environment.
Monitoring Changes with KQL Queries
Once Entra PM is running in “Controller” mode, you can use Kusto Query Language (KQL) queries to monitor changes made by the Enterprise Application. KQL queries allow you to analyze Azure Activity Logs and filter events based on specific criteria, such as the Application ID or the type of action performed.
For example, the following KQL query lists all changes made by the Enterprise Application:
// Read the Azure Resource Roles from Github
let AZRoleID = externaldata(Name:string, Id:guid )
[
@"https://raw.githubusercontent.com/Kaidja/AzureActiveDirectory/main/AzureRoles.json"
]
with(format="multijson");
// Define the CIEM APP ID. Replace the placeholder with your actual Application ID from the Azure AD portal
let CIEMAPPID = "DEFINE YOUR OWN VALUE HERE";
AzureActivity
| extend Action = (parse_json(Authorization)).action
// Take out only write actions
| where Action == "Microsoft.Authorization/roleAssignments/write"
// Filter based on the APP ID
| where Caller == CIEMAPPID
// Start only
| where ActivityStatusValue == "Start"
// Get the Subscription ID
| extend SubscriptionID = (parse_json(Properties)).subscriptionId
// Get the RequestBody
| extend RequestBody = parse_json(tostring(parse_json(Properties).requestbody))
| extend Scope = RequestBody.properties.scope
| extend RoleDefinitionId = RequestBody.properties.roleDefinitionId
| extend Id = tostring(split(RequestBody.properties.roleDefinitionId,"/")[6])
// Join the Azure Resource Roles tables to get the real Role Name
| join kind = inner(
AZRoleID
| extend Id = tostring(Id)
) on Id
// Print out the results
| project TimeGenerated,Caller,Action,Scope,Name,Id,RoleDefinitionId
This query retrieves the Azure Resource Roles from GitHub, filters the AzureActivity data based on the Application ID, and displays the results in a tabular format.
Leveraging Entra PM for Enhanced Security
By using Entra PM in “Controller” mode and monitoring changes with KQL queries, you can gain greater visibility into your Azure environment and improve the overall security posture. By keeping track of role assignments and access control changes, you can detect and address potential security risks more effectively. Furthermore, Entra PM’s centralized management capabilities enable you to maintain a more consistent and secure environment, reducing the likelihood of unauthorized access or data breaches.
Conclusion
Microsoft Entra Permission Management in “Controller” mode is a powerful and flexible solution for managing access control in your Azure environment. By leveraging its capabilities, you can streamline your workflows, gain better visibility into your environment, and enhance your security posture. Don’t forget to monitor changes using KQL queries to stay on top of any modifications made by the Enterprise Application. With Entra PM at your disposal, you can confidently manage and secure your Azure resources.