If you’re a Microsoft Defender XDR user, I highly recommend checking out the new Exposure Management feature. It offers extensive data that can greatly enhance your security landscape management—definitely worth exploring.
In this concise post, I’ll provide some KQL queries that help identify key resources within your network.
Microsoft Configuration Manager Servers
ExposureGraphNodes
| where set_has_element(Categories, "device")
| extend DeviceRoles = parse_json(NodeProperties.rawData.deviceRole)
| where DeviceRoles contains "MicrosoftConfigurationManager"
Active Directory Certificate Services
ExposureGraphNodes
| where set_has_element(Categories, "device")
| extend DeviceRoles = parse_json(NodeProperties.rawData.deviceRole)
| where DeviceRoles contains "ActiveDirectoryCertificateServicesServer"
Azure AD Connect / Entra Connect Servers
ExposureGraphNodes
| where set_has_element(Categories, "device")
| extend DeviceRoles = parse_json(NodeProperties.rawData.deviceRole)
| where DeviceRoles contains "AzureADConnectServer" or DeviceRoles contains "EntraConnectServer"
Exchange Servers
ExposureGraphNodes
| where set_has_element(Categories, "device")
| extend DeviceRoles = parse_json(NodeProperties.rawData.deviceRole)
| where DeviceRoles contains "ExchangeServer"
Active Directory Domain Controllers
ExposureGraphNodes
| where set_has_element(Categories, "device")
| extend DeviceRoles = parse_json(NodeProperties.rawData.deviceRole)
| where DeviceRoles contains "DomainController"
List All Servers
ExposureGraphNodes
| where set_has_element(Categories, "device")
| extend DeviceType = parse_json(NodeProperties.rawData.deviceType)
| where DeviceType == "Server"
List All Azure Arc for Servers
ExposureGraphNodes
| where EntityIds contains "microsoft.hybridcompute"
List All Azure VMs
ExposureGraphNodes
| where EntityIds contains "microsoft.compute"
| where NodeLabel == "microsoft.compute/virtualmachines"
List All Azure VMs Public IP Addresses
ExposureGraphNodes
| where EntityIds contains "microsoft.compute"
| where NodeLabel == "microsoft.compute/virtualmachines"
| extend PublicIP = parse_json(NodeProperties.rawData.publicIP)
| project NodeName,PublicIP
How can I use that data?
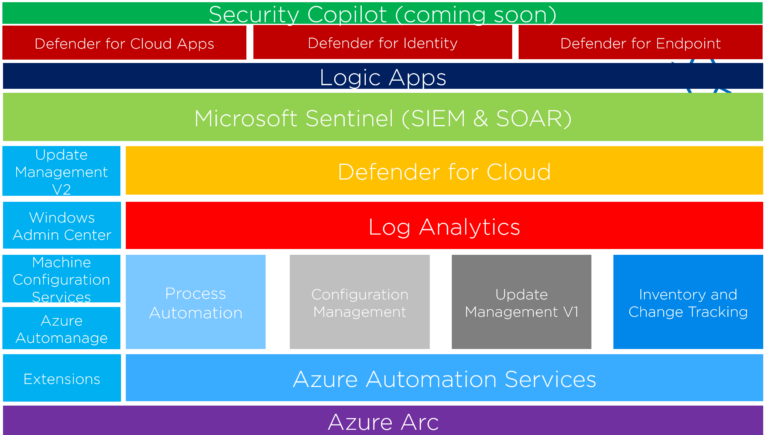
By analyzing the data from these queries, you can tag and categorize resources like Azure VMs or Azure Arc for Servers, which facilitates targeted management and enhances security oversight. Implementing automation based on these tags can trigger specific policies or actions, increasing efficiency and responsiveness.
Additionally, integrating this data into Azure Workbooks allows for dynamic reporting and analytics, providing real-time insights into the security status of your environment. This strategic use of data not only streamlines operations but also strengthens your overall security framework.